Zero-Trust on AWS: What BeyondCorp Actually Requires Beyond IAM Policies
Zero-trust is not 'add MFA and call it done.' This is what a real identity-driven, continuously-verified AWS network architecture looks like in CDK.

Zero-trust security is no longer optional. As modern infrastructure becomes increasingly distributed across microservices, remote teams, SaaS platforms, and hybrid networks, traditional “trusted networks” and perimeter-based defense models are obsolete.
This blog walks through a fully production-ready Zero-Trust Network Architecture (ZTNA) on AWS, inspired by Google’s BeyondCorp principles and implemented through AWS CDK (TypeScript).
It is based on the project:
InfraTales | Zero-Trust Network – BeyondCorp Security Architecture on AWS, created by Rahul Ladumor.
If you want an enterprise-grade zero-trust foundation, least privilege, continuous verification, micro-segmentation, identity-based access, and end-to-end encryption, this guide is your blueprint.
What Is Zero-Trust? (In Practical Engineering Terms)
Zero-trust follows one simple idea:
Never Trust, Always Verify — every request, every time, regardless of network location.
Instead of relying on “safe internal networks,” every request is validated by:
- Strong identity authentication
- Device posture
- Contextual risk
- Continuous authorization
- Micro-segmentation
This project turns these principles into deployable AWS infrastructure using IaC (Infrastructure as Code).
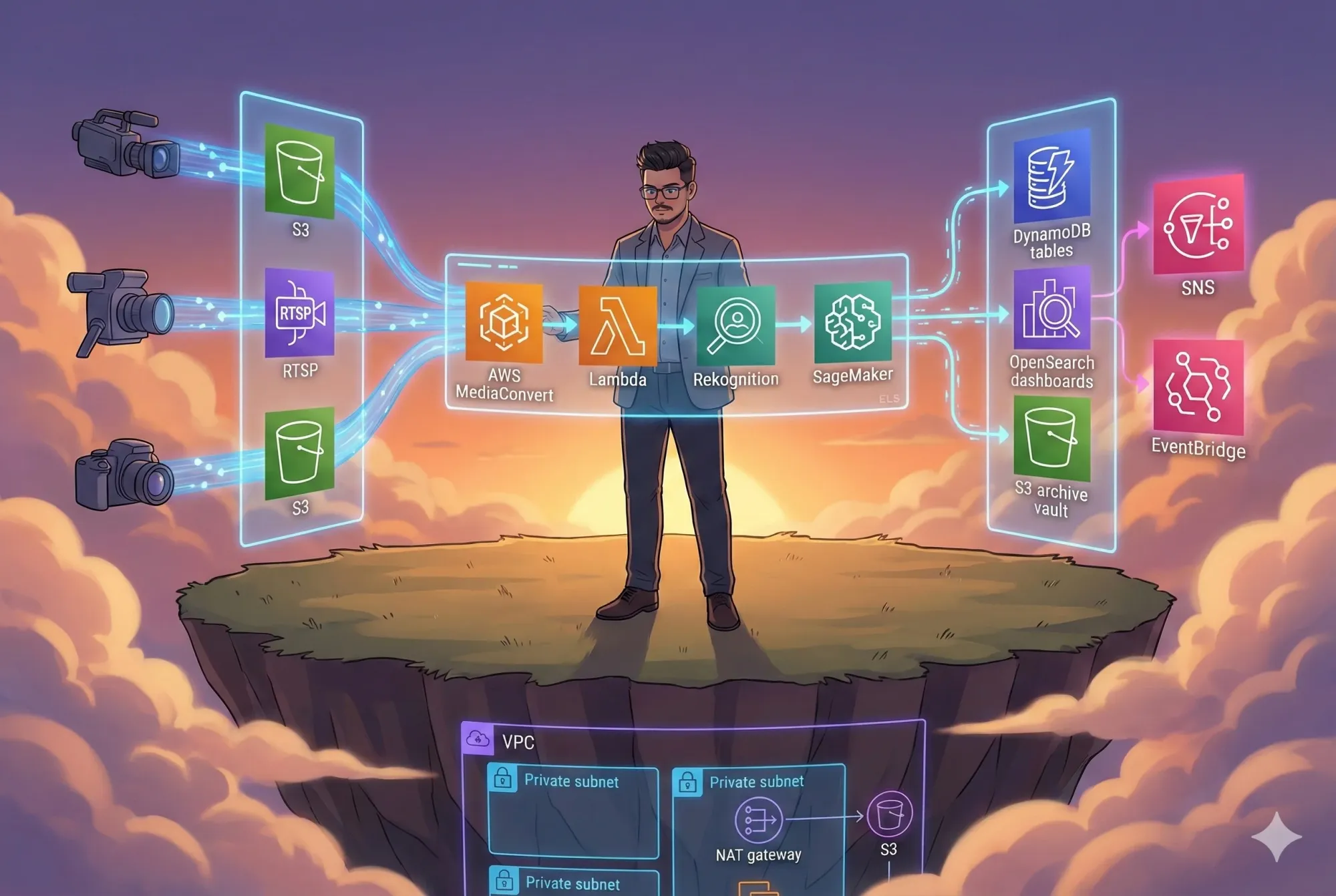
Production Architecture Overview
The architecture combines:
- Identity-based access (IAM, OIDC, STS)
- Micro-segmentation (VPC, subnets, SGs)
- Application-level verification (WAF, API Gateway auth)
- Continuous monitoring (CloudWatch, X-Ray)
- Private access to AWS services (VPC Endpoints)
- Zero-trust edge layer (WAF + CloudFront + LB)
Here’s the architecture:
System Architecture

Zero-Trust Principles Applied to AWS
1. Identity as the Primary Control Plane
- IAM roles, STS tokens, SigV4 signing
- No implicit network trust
- Private resources are only reachable via identity-based policies
2. Micro-segmentation
- Separate subnets for public, private, and data tiers
- Explicit security group rules
- No lateral movement possible
- VPC Endpoints eliminate the need for public AWS service traffic
3. Continuous Verification
- WAF evaluates every request
- API Gateway performs auth checks
- CloudWatch alarms + X-Ray trace anomalies
- Runtime validation at each layer
4. Least-Privilege Access Everywhere
- IAM roles with scoped permissions
- KMS encryption per resource
- S3 bucket policies restricted to VPC endpoints
- Lambda/ECS access is tightly controlled
Deep-Dive: Network Foundation (VPC Architecture)
The network is fully isolated and Multi-AZ for high availability.
VPC Design

Key Network Security Features
✔️ No database subnet has internet access
✔️ All outbound-only private traffic goes through NAT
✔️ VPC endpoints remove need for public AWS access
✔️ WAF & LB live in public subnets
✔️ Application workloads run in private subnets
Data Flow: How a Request Moves Through Zero-Trust

Deployment: Fully Automated with AWS CDK
The project uses:
- TypeScript CDK
- Environment-based config (dev/stage/prod)
- Automated testing (unit + integration)
- Infrastructure validation
Deploy Example
# Install CDK
npm install -g aws-cdk
# Configure AWS credentials
aws configure
# Deploy to dev
ENVIRONMENT_SUFFIX=dev cdk deploy
# Deploy to production
ENVIRONMENT_SUFFIX=prod cdk deploy
This diagram outlines the CI/CD release workflow: Code push → build → test → deploy to staging → canary rollout → health checks → full production deployment or rollback. Ensures secure, controlled, and automated releases with zero-trust governance.
This enables immutable, repeatable, secure deployments.
Observability: Continuous Monitoring & Threat Detection
✔ CloudWatch dashboards
✔ Distributed tracing with AWS X-Ray
✔ Log insights queries
✔ SNS alerts on anomalies
✔ VPC Flow Logs (network visibility)
This is where “continuous verification” comes alive. Zero-trust is meaningless without strong telemetry.
Security Hardening (Production Checklist)
✔ End-to-end TLS (TLS 1.3)
✔ KMS encryption for S3, RDS, DynamoDB
✔ IAM least-privilege everywhere
✔ WAF + rate limiting + threat rules
✔ Secrets Manager (no plaintext secrets)
✔ VPC isolation
✔ CloudTrail audit logs enabled
This design meets requirements for:
- SOC 2
- NIST 800-207 (Zero Trust Architecture)
- PCI-DSS (with additional workload hardening)
- ISO 27001
Cost Overview (Realistic Estimates)
| Environment | Cost Range |
|---|---|
| Development | $190 – $550 / month |
| Production | $900 – $4,000 / month |
Cost drivers:
- NAT Gateways
- EC2/ECS compute
- RDS instances
- CloudWatch logs
- Data transfer
Optimizations include:
- Spot instances
- S3 Intelligent-Tiering
- Automated shutdown of non-prod
- Right-sizing
Why This Architecture Matters
This design delivers:
True Zero-Trust Security
Identity-based access, continuous verification, and micro-segmentation.
Enterprise-Ready Infrastructure
Multi-AZ, highly available, production-secure.
Infrastructure as Code
Fully automated, testable, repeatable deployments.
Scalability & Cost Efficiency
Auto-scaling, optimized workloads, intelligent storage.
This is a reference architecture suitable for:
- FinTech
- SaaS platforms
- Enterprises adopting BeyondCorp
- Regulated workloads
- Multi-environment cloud platforms
Final Thoughts
This Zero-Trust Network Architecture is a complete, production-grade blueprint that transforms AWS infrastructure into a secure, identity-driven environment.
It blends Google’s BeyondCorp model with AWS-native capabilities, making it one of the most practical zero-trust implementations available today.
If you’re building modern cloud systems where security, scalability, and automation matter, this architecture is the perfect foundation.
🔗 Amazon VPC - https://docs.aws.amazon.com/vpc/latest/userguide/what-is-amazon-vpc.html
🔗 VPC Endpoints - https://docs.aws.amazon.com/vpc/latest/privatelink/vpc-endpoints.html
🔗 AWS WAF - https://docs.aws.amazon.com/waf/latest/developerguide/what-is-aws-waf.html
🔗 Amazon CloudFront - https://docs.aws.amazon.com/AmazonCloudFront/latest/DeveloperGuide/Introduction.html
🔗 Amazon API Gateway - https://docs.aws.amazon.com/apigateway/latest/developerguide/welcome.html
🔗 AWS IAM - https://docs.aws.amazon.com/IAM/latest/UserGuide/introduction.html
🔗 AWS STS (Identity Tokens) - https://docs.aws.amazon.com/STS/latest/APIReference/welcome.html
🔗 AWS Lambda - https://docs.aws.amazon.com/lambda/latest/dg/welcome.html
🔗 Amazon ECS - https://docs.aws.amazon.com/AmazonECS/latest/developerguide/Welcome.html
🔗 Amazon EC2 - https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/concepts.html
🔗 Amazon RDS - https://docs.aws.amazon.com/AmazonRDS/latest/UserGuide/Welcome.html
🔗 Amazon DynamoDB - https://docs.aws.amazon.com/amazondynamodb/latest/developerguide/Welcome.html
🔗 Amazon S3 - https://docs.aws.amazon.com/AmazonS3/latest/userguide/Welcome.html
🔗 AWS KMS Encryption - https://docs.aws.amazon.com/kms/latest/developerguide/overview.html
🔗 AWS Secrets Manager - https://docs.aws.amazon.com/secretsmanager/latest/userguide/intro.html
🔗 AWS CloudWatch - https://docs.aws.amazon.com/cloudwatch/
🔗 AWS X-Ray - https://docs.aws.amazon.com/xray/latest/devguide/aws-xray.html
🔗 AWS CloudTrail - https://docs.aws.amazon.com/awscloudtrail/latest/userguide/cloudtrail-user-guide.html
🔗 CDK for TypeScript - https://docs.aws.amazon.com/cdk/latest/guide/home.html
👉 GitHub Repository:
https://github.com/InfraTales/zero-trust-network-architecture